Manual Alarm
Employees, visitors, and external personnel can request help instantly in emergency situations: via the app, a widget, or a wearable Bluetooth button.
Time Alarm (Dead Man’s Switch)
Regular check-ins ensure user safety. If no response is detected, an alarm is triggered automatically.
Silent Alarm
Provides discreet protection in critical situations. The alarm can be activated unnoticed, remains inaudible to others, and immediately requests assistance.
Inactivity Alarm
If no activity is detected within a defined time frame, an alarm is triggered automatically.
Central Alarm
In critical situations, the central alarm enables coordinated evacuations. All individuals are informed simultaneously and guided to take appropriate action.
Technical Alarm
Visual and acoustic alerts in case of system issues, such as loss of internet connectivity.
Pre-Alarm
Audible pre-warning signals help prevent false alarms and allow users to cancel an alert before it is triggered.
Alerting & Notification
All defined alert chains and emergency contacts are notified immediately. Relevant information about the incident is available in real time.
Position-Based Alarm
Integrated sensors detect critical events such as falls or loss of consciousness and automatically trigger the defined emergency process.
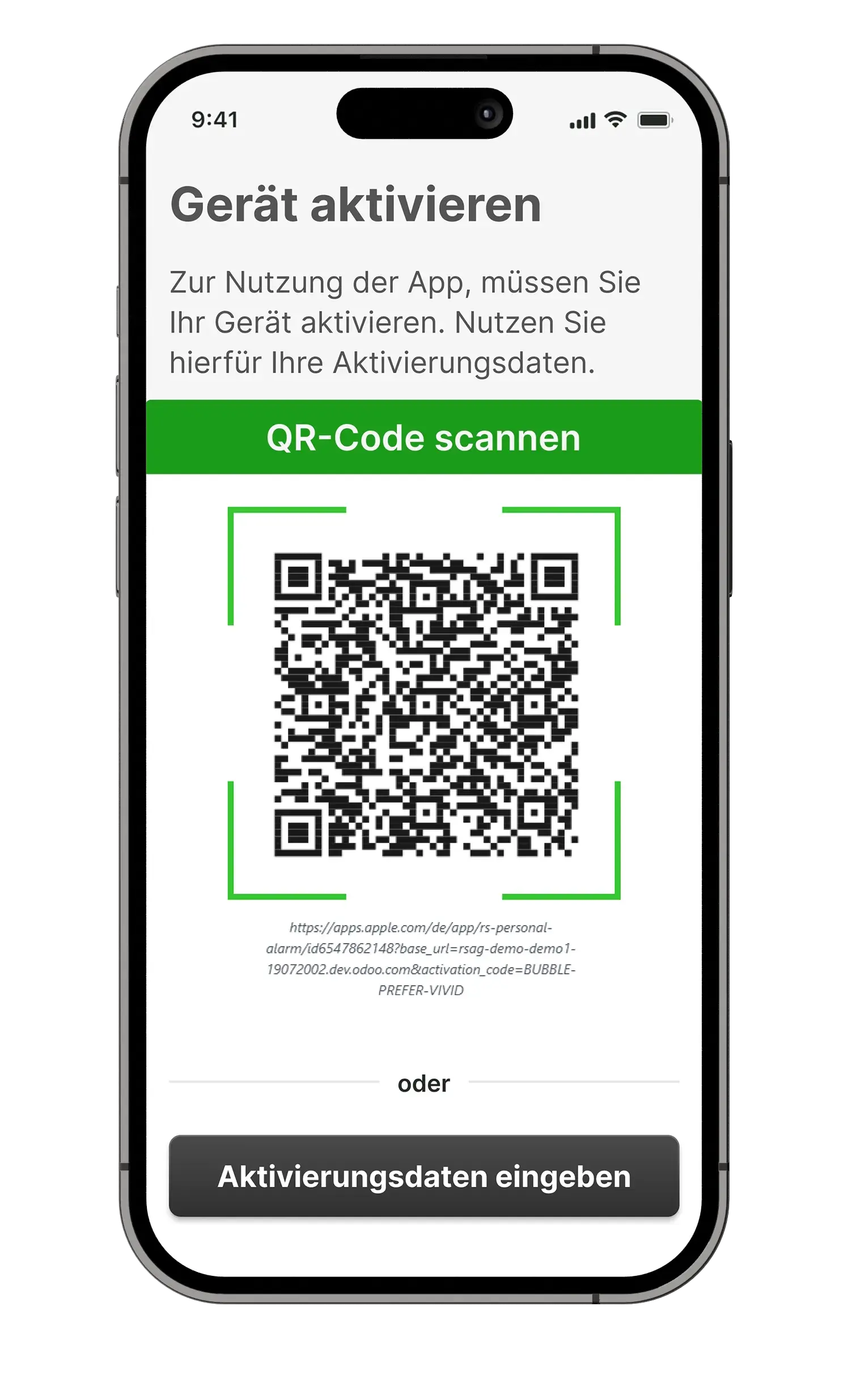
Easy Onboarding
Visitors or external personnel simply scan a QR code and are automatically assigned to the correct group and safety configuration.
Manual Alarm
Employees, visitors, and external personnel can
request help instantly in emergency situations: via the app, a widget, or a wearable Bluetooth button.
Time Alarm (Dead Man’s Switch)
Regular check-ins ensure user safety. If no response is detected, an alarm is triggered automatically.
Silent Alarm
Provides discreet protection in critical situations. The alarm can be activated unnoticed, remains inaudible to others, and immediately requests assistance.
Inactivity Alarm
If no activity is detected within a defined time frame, an alarm is triggered automatically.
Technical Alarm
Visual and acoustic alerts in case of system issues, such as loss of internet connectivity.
Central Alarm
In critical situations, the central alarm enables coordinated evacuations. All individuals are informed simultaneously and guided to take appropriate action.
Pre-Alarm
Audible pre-warning signals help prevent false alarms and allow users to cancel an alert before it is triggered.
Alerting & Notification
All defined alert chains and emergency contacts are notified immediately. Relevant information about the incident is available in real time..
Position-Based Alarm
Integrated sensors detect critical events such as falls or loss of consciousness and automatically trigger the defined emergency process.
Easy Onboarding
Visitors or external personnel simply scan a QR code and are automatically assigned to the correct group and safety configuration.
den QR-Code scannen und sind automatisch der korrekten Personengruppe zugeordnet und abgesichert.

2. Processing in the Receiving Unit

3. Activation of Alert Chain

4. Notification of First Responders

1. Alarm Trigger
Emergency Process Flow

2. Processing in the Receiving Unit

3. Activation of Alert Chain

4. Notification of First Responders

1. Alarm Trigger
Emergency Process Flow
1. Alarm Trigger
An alarm is triggered manually or automatically depending on the situation.
2. Processing in the Receiving Unit
The system automatically initiates the predefined alert chain.
3. Activation of Alert Chain
All first responders or emergency contacts (internal or external) are notified via app, phone, SMS, or email.
4. Notification of First Responders
Responders receive all relevant information about the incident, affected person, and location immediately.
1. Alarm Trigger
An alarm is triggered manually or automatically depending on the situation.
2. Processing in the Receiving Unit
The system automatically initiates the predefined alert chain.
3. Activation of Alert Chain
All first responders or emergency contacts (internal or external) are notified via app, phone, SMS, or email.
4. Notification of First Responders
Responders receive all relevant information about the incident, affected person, and location immediately.
Precise location tracking indoor and outdoor
Precise location tracking indoor and outdoor
Outdoor location tracking via GPS
GPS satellites allow for very precise location determination in outdoor areas – available on almost all smartphones or emergency buttons with GPS support.
Indoor location tracking via bluetooth beacons
Indoor emergencies can be precisely located using bluetooth beacons. You can choose to use your own transmitters or our beacons with extra-long battery life.

Indoor location tracking via WLAN
With an existing network of multiple WLAN access points, precise location tracking is possible even without satellite reception or additional hardware.
Geofencing (Beta)
Geofencing creates a virtual boundary around a real location and automatically triggers actions when a person or device enters or leaves that area.
Outdoor location tracking via GPS
GPS satellites allow for very precise location determination in outdoor areas – available on almost all smartphones or emergency buttons with GPS support.
Indoor location tracking via bluetooth beacons
Indoor emergencies can be precisely located using bluetooth beacons. You can choose to use your own transmitters or our beacons with extra-long battery life.

Indoor location tracking via WLAN
With an existing network of multiple WLAN access points, precise location tracking is possible even without satellite reception or additional hardware.
Geofencing (Beta)
Geofencing creates a virtual boundary around a real location and automatically triggers actions when a person or device enters or leaves that area.
Instant Protection – Fully Anonymous
Instant Protection – Fully Anonymous
Easy Onboarding
No account, registration, or login required. Simply scan the QR code, install the app, and be protected instantly.
QR codes can be generated for different groups. With one scan, users are automatically assigned to the correct group, including predefined alert chains and safety protocols.
RS Personal Alarm can be used fully anonymously. Movement data is processed temporarily, encrypted, and automatically deleted after use.
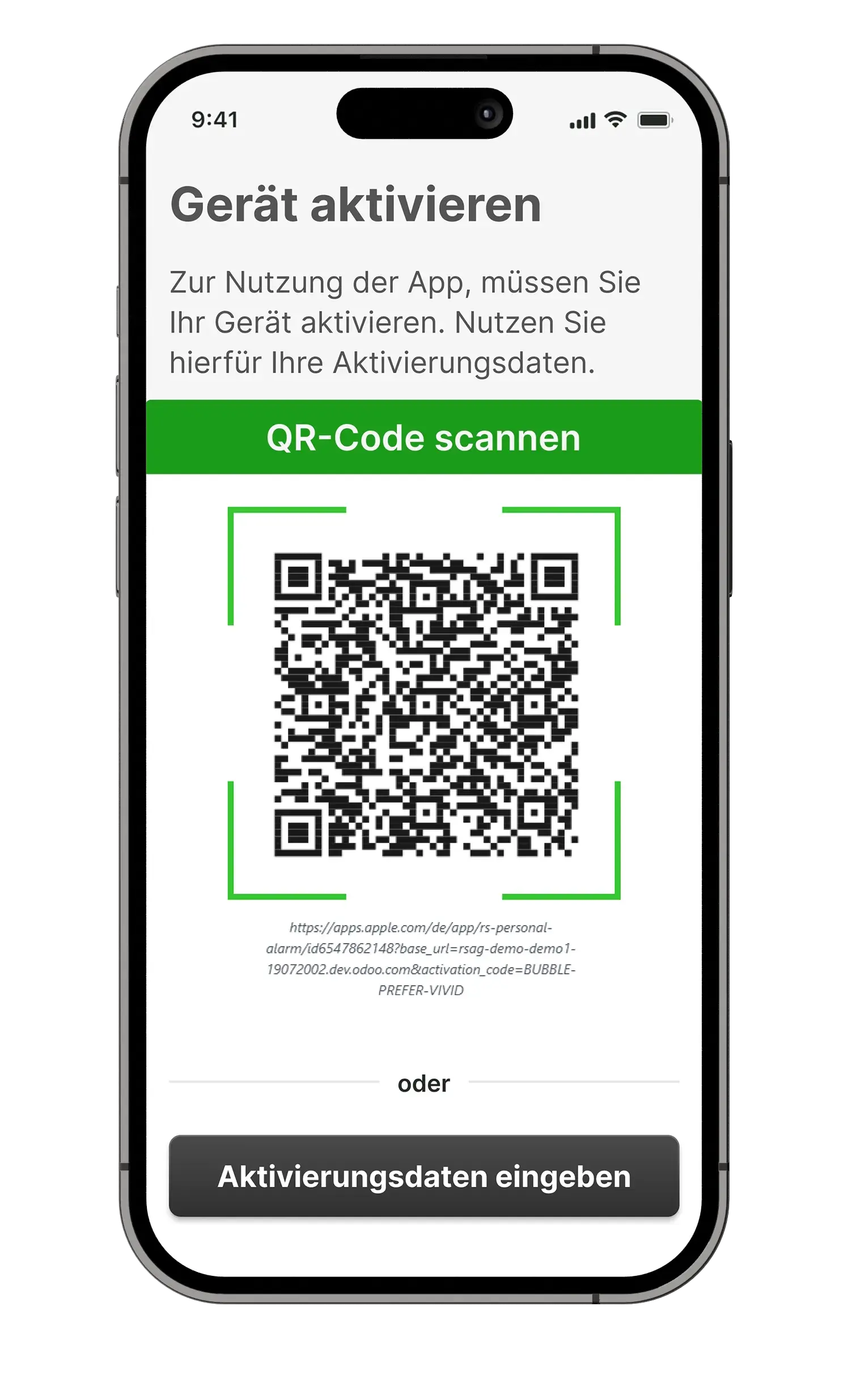
Easy Onboarding
No account, registration, or login required. Simply scan the QR code, install the app, and be protected instantly.
QR codes can be generated for different groups. With one scan, users are automatically assigned to the correct group, including predefined alert chains and safety protocols.
RS Personal Alarm can be used fully anonymously. Movement data is processed temporarily, encrypted, and automatically deleted after use.
Central Management & Monitoring
Central Management & Monitoring
Central Control Unit
All emergency alerts and responses are managed and monitored centrally.
Access Control
Only authorized users can configure settings such as alert chains.

Groups & Profiles
Different user groups with specific risk profiles can be defined and managed.
Central Control Unit
All emergency alerts and responses are managed and monitored centrally.
Access Control
Only authorized users can configure settings such as alert chains.

Groups & Profiles
Different user groups with specific risk profiles can be defined and managed.
Your Benefits
Employees, visitors, and external personnel can install the app directly on their smartphones. No additional devices or external hardware are required. The receiving unit (RU) is web-based, requires no installation on your system or computer, and can be configured and ready for use within just a few hours.
The system provides you with enough flexibility to tailor it precisely to the needs of your business. We are happy to handle the configuration - you don't have to do anything else.
Our solution has been developed in accordance with DGUV Rule 112-139 (formerly BGR/GUV-R 139) and the requirements of DIN VDE V 0825-11.
The location of individuals is hidden by default and is only shared in the event of an emergency. Movement data is collected only temporarily, processed in encrypted form, and automatically deleted once the app is closed. Employees are not monitored.
All data is processed solely for its intended purpose and in full compliance with GDPR. The receiving unit is hosted exclusively on servers located in Germany.
Your Benefits
Employees, visitors, and external personnel can install the app directly on their smartphones. No additional devices or external hardware are required. The receiving unit (RU) is web-based, requires no installation on your system or computer, and can be configured and ready for use within just a few hours.
The system provides you with enough flexibility to tailor it precisely to the needs of your business. We are happy to handle the configuration - you don't have to do anything else.
Our solution has been developed in accordance with DGUV Rule 112-139 (formerly BGR/GUV-R 139) and the requirements of DIN VDE V 0825-11.
The location of individuals is hidden by default and is only shared in the event of an emergency. Movement data is collected only temporarily, processed in encrypted form, and automatically deleted once the app is closed. Employees are not monitored.
All data is processed solely for its intended purpose and in full compliance with GDPR. The receiving unit is hosted exclusively on servers located in Germany.
Free Demo
Simply let us know how many people you would like to protect with RS Personal Alarm,
and we will provide you with a tailored offer.


Free Demo
Simply let us know how many people you would like to protect with RS Personal Alarm, and we will provide you with a tailored offer.


